Description
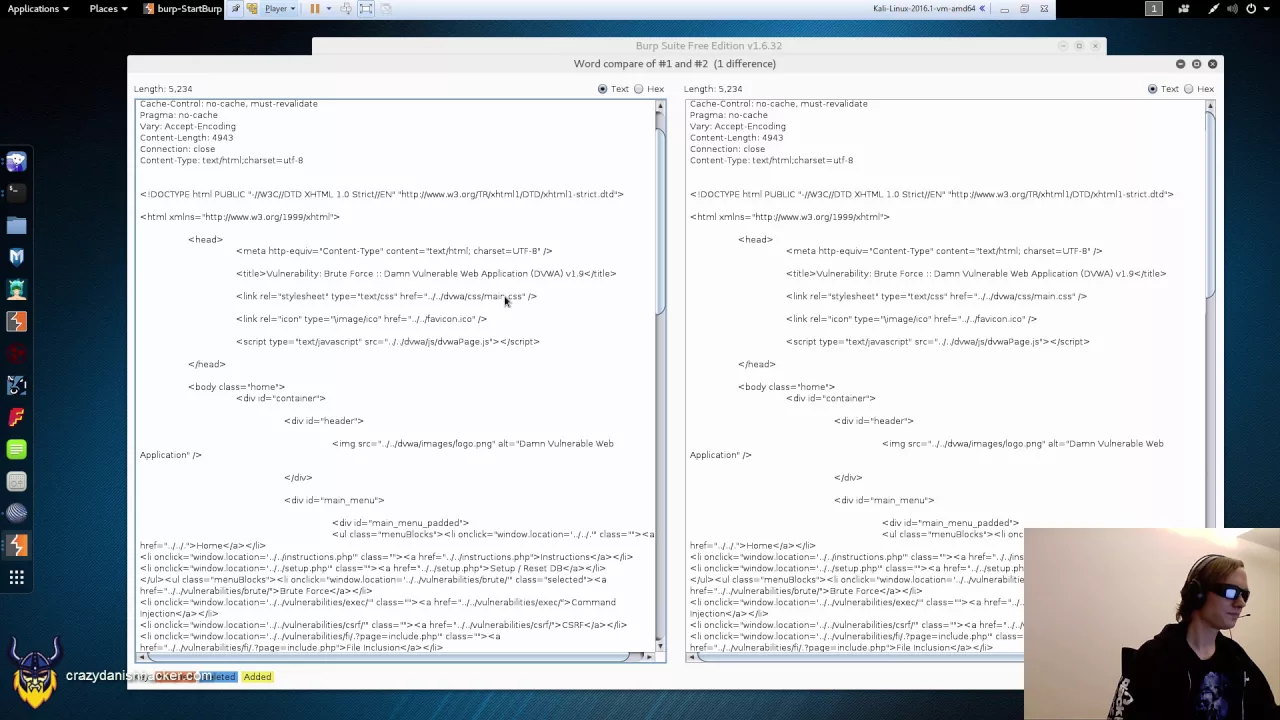
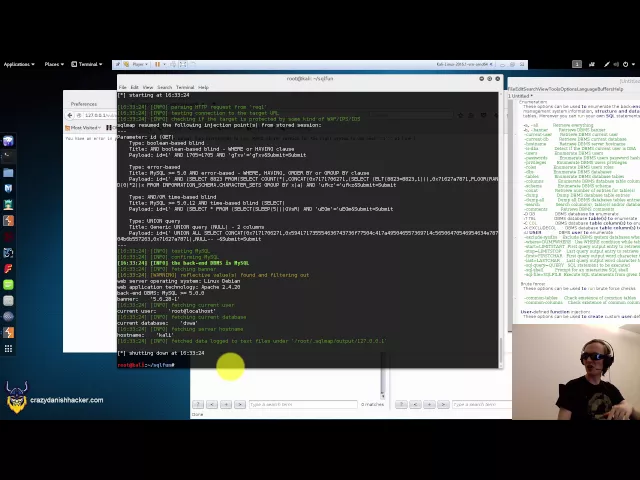
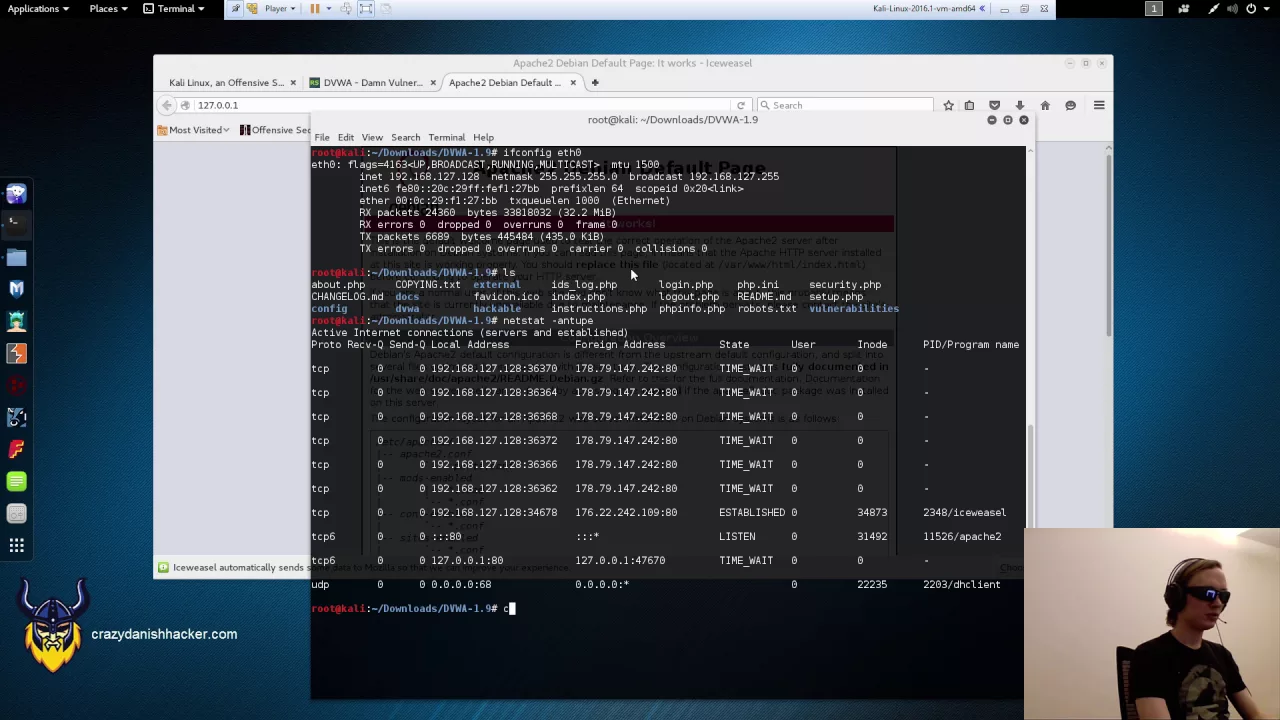
In this video I demonstrate how to perform a Cross-Site Request Forgery (i.e. CSRF or C-Surf) attack. This type of CSRF attack forces a logged-in user to change their password, without them knowing, when a malicious page is viewed. The malicious page can be viewed in multiple ways by a legitimate user (not covered in this video, be creative, think like a hacker).
Anything that is not protected by CSRF tokens and the HTTP referer in combination (the referer header alone does not provide adequate protection), is subject to attack. While functions such as changing a user’s password may be of interest, administrative functions that allow the admin to e.g. execute or modify code, are at even higher risk of being targeted by a malicious attacker.
Most modern web applications have protections against this type of attack, and viewers of this video should not worry too much (or at all) about this type of attack being executed against them, as it has several prerequisites that needs to be fulfilled.
Topics covered:
– Cross-Site Request Forgery (CSRF/C-Surf)
– Automatic Form Submit (JavaScript)
– Basic HTML
Stay tuned and subscribe for more upcoming videos showing actual hacks!

Recent Comments